Difference between revisions of "Sentry SSO with JIRA"
(→Setup SSO on JIRA) |
|||
| Line 18: | Line 18: | ||
[[File:JIRA SAML Bitium plugin.JPG|1000px]] | [[File:JIRA SAML Bitium plugin.JPG|1000px]] | ||
| − | [[File:JIRA SAML Bitium plugin installed.JPG | + | [[File:JIRA SAML Bitium plugin installed.JPG]] |
[[File:JIRA SAML Bitium plugin settings system security SAML config.JPG|1000px]] | [[File:JIRA SAML Bitium plugin settings system security SAML config.JPG|1000px]] | ||
[[File:JIRA SAML Bitium plugin settings system security SAML.JPG|1000px]] | [[File:JIRA SAML Bitium plugin settings system security SAML.JPG|1000px]] | ||
Revision as of 10:02, 18 August 2017
Contents
Introduction
This document describes how to configure on-premise Atlassian JIRA to work with Sentry SSO. Before following these instructions, you should be familiar with using Sentry - see the Sentry User Guide for more information.
Setup AuthControl Sentry Keys
Before you are able to create a Single Sign On configuration on your JIRA site, you will need to setup some Keys. Please see a separate article: HowToCreateKeysOnCmi. You will need the certificate you generate in a later section of this article. This can be retrieved from the View Keys menu option of Swivel AuthControl Sentry.
Setup SSO on JIRA
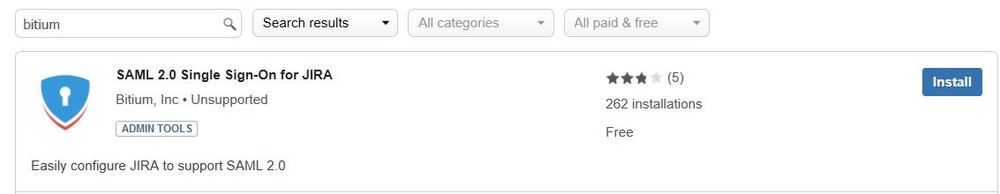
To configure SSO on JIRA a third party add-on is required. There are many SAML plugins available but the plugin that has been used by one of our partners and integrated successfully is the "SAML 2.0 Single Sign-On for JIRA" plugin by Bitium, Inc.
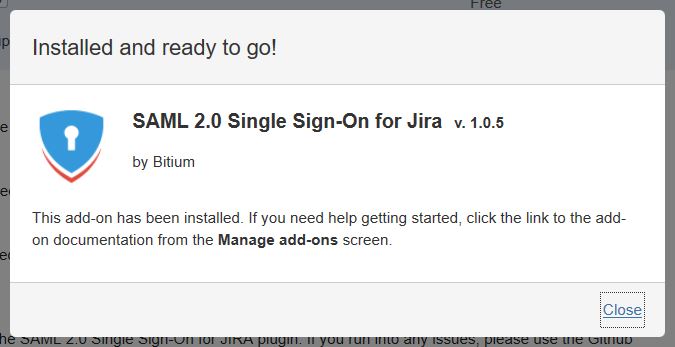
Download and install this plugin.
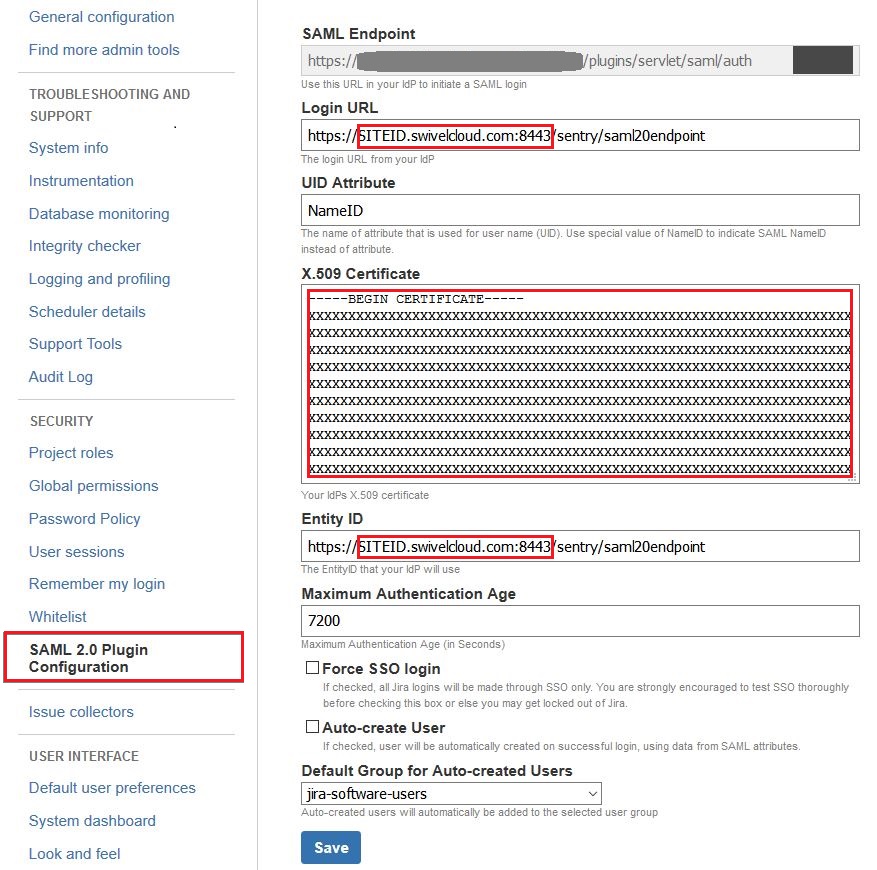
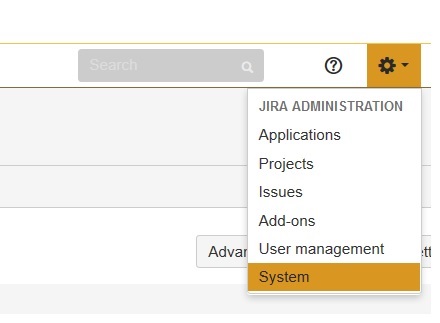
Now navigate to your AuthControl Sentry View IdP Metadata page and copy the content of this page.
Click save. You will see something like the below. Click save again.
Setup AuthControl Sentry Application definition
Login to the AuthControl Sentry Administration Console. Click Applications in the left hand menu. To add a new Application definition for JIRA, click the Add Application button and select SAML - JIRA type.
Name: JIRA
Points: 100 (the number of points the user needs to score from their Authentication Method in order to successfully authenticate to this Application)
Portal URL: URL to access to JIRA (It does not require modification)
Entity ID: Identifier of the JIRA SAML request (It does not require modification)
Federated Id: email
Setup AuthControl Sentry Authentication definition
As an example here we will be using Turing authentication as the Primary method required for JIRA authentication.
Login to the AuthControl Sentry Administration Console. Click Authentication Methods in the left hand menu. Click the Edit button against the Turing option in the list of Authentication Methods. Give this Authentication Method 100 points. This will mean that when a login attempt is made to the JIRA Application, this Authentication Method will be offered during login. (Please read about AuthControl Sentry Rules and familiarize your self with AuthControl Sentry here )
Testing authentication to Google via Swivel AuthControl Sentry
This should be the final step after all previous elements have been configured.
Visit your AuthControl Sentry Page with your public DNS entry of your Swivel AuthControl Sentry server, e.g. https://mycompanysentrydomain/sentry/startPage. On a Start Page you will be able to see a new JIRA Icon on which you can click and proceed with authentication (as you would by going straight to the JIRA page)
When you visit this URL you will notice that the domain should redirect to the identity provider login URL that you setup.
Once you have submitted your username. You should be presented with the Sentry username page.
In this login example we are using the email as a username.
Once you have submitted your username. You should be presented with the page of the Authentication Method which can score enough points to match the points required by the JIRA Application definition.
After we enter our authentication credentials we successfully will see the JIRA account that we tried to access.
Troubleshooting
There are various logging components available for this particular integration which can aid in diagnosis at different points during authentication.
The Swivel Core has a Log Viewer menu item which can reveal information concerning user status e.g. is the user locked, has a session been started for the image request; The Swivel AuthControl Sentry has a View Log menu item which provides details about the SAML assertion and response received from JIRA and can be useful for comparison with the Google SAML Assertion Validator output;
It is crucial when troubleshooting, to pinpoint where the authentication is failing. For example, you may find that the Swivel Core logs show a successful authentication (which would indicate that the user has entered their Password and OTC correctly), but the AuthControl Sentry logging shows that there is a problem with the SAML assertion.
Two common issues which can be diagnosed with the validator are:
Certificate or decryption issues;
Can AuthControl Sentry find the Certificate locally, is it the correct one?
Has the correct Certificate been uploaded to JIRA?
Does the Repository -> Attribute name being used actually map to a Repository attribute? Has a User Sync occurred in the Swivel Core since modifying this?