Joomla 1.6 Integration
Contents
Introduction
This document describes steps to configure Joomla with PINsafe as the authentication server.
To use the Single Channel Image such as the TURing Image, the PINsafe server must be made accessible. The client requests the images from the PINsafe server, and is usually configured using Network Address Translation, often with a proxy server. The Swivel virtual or hardware appliance is configured with a proxy port to allow an additional layer of protection.
Prerequisites
Joomla 1.6
PINsafe 3.x
Joomla RADIUS Authentication plugin available here Registration required.
When using the TURing, Security String Index or Message Confirmed, the required images are requested by the client from the PINsafe server. This is usually carried out through a NAT to the PINsafe server.
The PINsafe Joomla integration script can be found here: PINsafe Joomla Integration Script
Baseline
Joomla 1.6
PINsafe 3.8
Architecture
Joomla makes authentication requests against the PINsafe server by RADIUS.
Swivel Configuration
Configuring the RADIUS server
On the Swivel Administration console configure the RADIUS Server and NAS, see RADIUS Configuration
Enabling Session creation with username
To allow the TURing image, PINpad and other single channel images, under Server/Single Channel set Allow session request by username to Yes.
Setting up Swivel Dual Channel Transports
Joomla RADIUS Configuration
A RADIUS module is used for Joomla authentication to authenticate to the PINsafe RADIUS server.
Joomla RADIUS Authentication Plug-in Installation
To install, on the Joomla Administration console select Extensions, then Extension Manager, there are 3 options for installation, select the desired installation method to upload the plugin:
- Upload Package File
- Install from Directory
- Install from URL
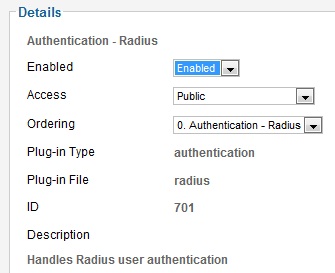
Joomla RADIUS Authentication Plug-in Configuration
When installation is complete on the Joomla Administration console select Extensions, then Plug-in Manager, the RADIU plug-in should be listed.
Click on the plugin, and set the following information:
Enabled Enables the plug-in
Access Which level of access the plugin-is applied to all
Ordering In which order authentication is to be made
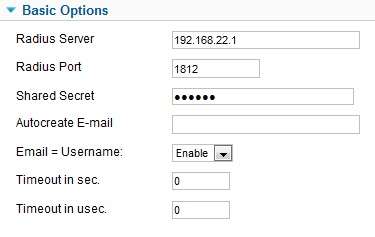
RADIUS Server The PINsafe server hostname or IP address
RADIUS Port The PINsafe server RADIUS port, usually 1812
Shared Secret The shared secret also entered onto the PINsafe server
other settings can be left as default depending on the required configuration
When complete save the settings, ensuring that the plugin is enabled.
Joomla RADIUS Authentication Plug-in Testing
Test the RADIUS module with a username and password or OTC. A RADIUS request should be seen on the PINsafe server. A valid OTC can be derived from the PINsafe Administration console for a user by selecting View Strings.
Joomla Login Page Customisation
The Joomla login page can be modified in a number of ways, such as:
- Generation of Single Channel Images, such as TURing
- SMS Message request buttons
- Security String Index to show which security string can be used
Creating a PINsafe login module
A PINsafe login module can be downloaded and installed using Joomla 1.6 PINsafe Module, or follow the instructions below to create a custom login module
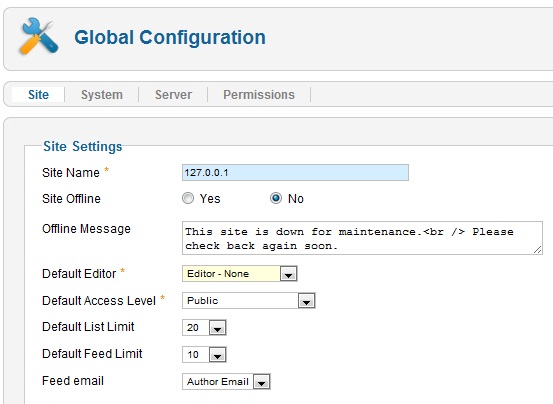
In order to configure the PINsafe script, the WYSIWYG editor needs to be temporarily disabled. To disable/enable the editor, on the Joomla Administration console select Site, then Global Configuration, and set the Default Editor to Editor-None. If an error is received then the Administration Console permissions need to be correctly set. See Cannot save Global Configuration changes
To create the new login module, on the Joomla Administration console select Extensions, then Module Manager. Click on New, and select a Module type of Custom HTML.
Adding the Custom Script
Under Custom output use enter the web page modification and script. The following lines need to be modified to reflect the environment
The following can be edited in the script to hide buttons that are not required:
TURing image button
<input type="button" value="TURing" onclick="showTuring();">
Show Security String Index button (To tell user which security string to use)
<input type="button" value="Index" onclick="showIndex();">
Message button to request a new security string to be sent to the user
<input type="button" value="Message" onclick="showMessage();">
The URL of the PINsafe server will also need to be modified to reflect the correct port and context.
For a virtual or hardware appliance installation:
pinsafeUrl = "https://turing.swivelsecure.com:8443/proxy/";
For a software only install see Software Only Installation
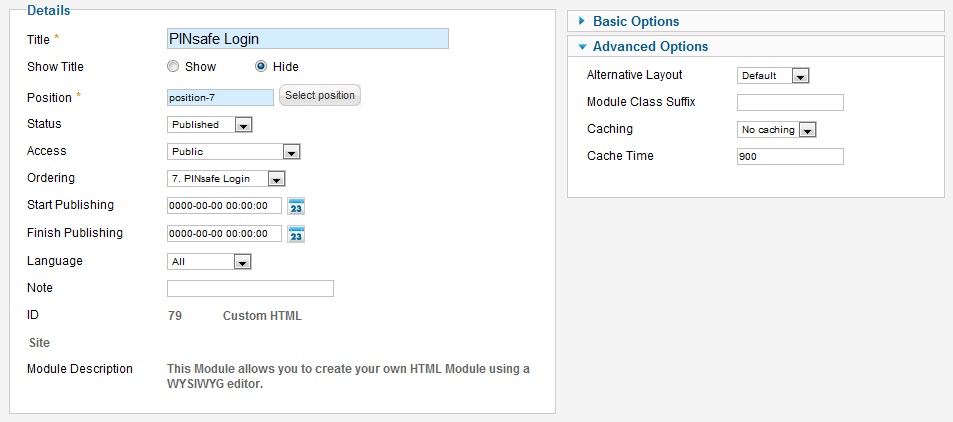
Configuring the PINsafe login module
Set the following details:
Title: PINsafe login. Descriptive Module Name
Show Title: Hide. Hides the Title in the login screen
Position: Position-7. This will vary according to the website design, and should be positioned close to the associated login module.
Status: published.
Access: Public. Select Access level appropriate
Ordering: 7. PINsafe Login. Where the PINsafe modification will appear in the login (this will depend on each site configuration)
Other settings can be left as default
Under Advanced Options, set Caching to None
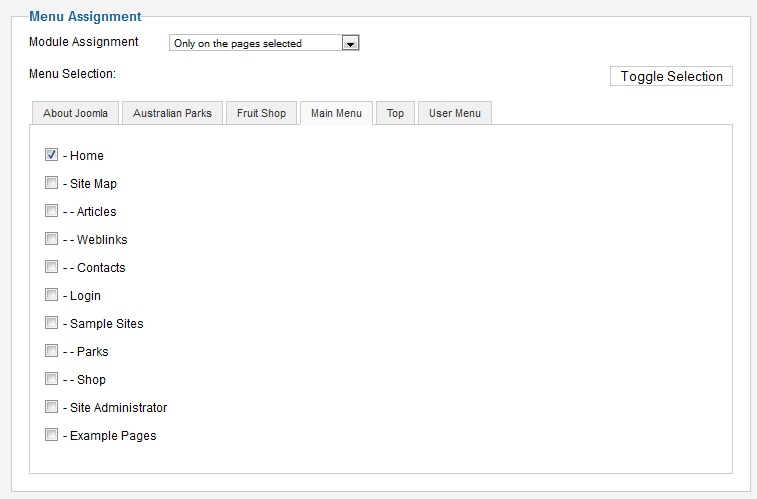
Menu Assignment
The module will need to be assigned, this will vary according to the site and page configuration. On the module, select Menu Assignment, then select the pages that are required. The below example uses the Module Assignment of 'Use only the pages selected' with Man Menu, Home selected.
Testing
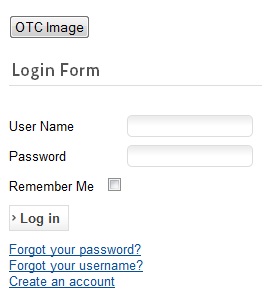
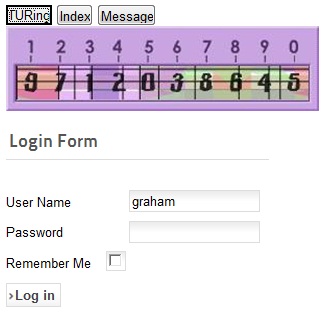
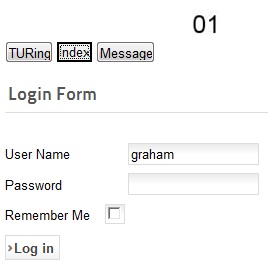
Connect to the Joomla website and verify that the correct images are shown
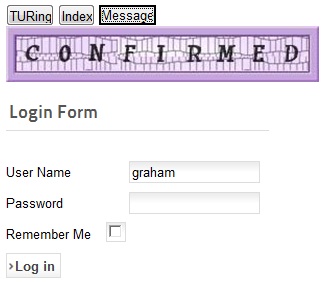
Login with TURing, String Index and Message Buttons
TURing Image Login
Security String Index for SMS Message login
SMS Message request Confirmed
Additional Configuration Options
Troubleshooting
Check the PINsafe logs for Turing images and RADIUS requests.
Known Issues and Limitations
None
Additional Information
For assistance in the PINsafe installation and configuration please firstly contact your reseller and then email Swivel Secure support at support@swivelsecure.com